Howdy, folks !
the following blog is the continuation of previous content, solving matasano with kotlin part 1 . In this post, i will talk about how to solve next two challenges in set 1 (challenge 3 to 4).
Challenge 3:
Description:The challenge expected us to create a program that crack a hex string that has been encrypted with single byte XOR. In order to solve this question you just need to reuse the code from challenge 2 and give some little bit of alteration.
I try to design the UI really simple so you guys don't have difficulty following the code.The following is the snipped code to solve the challenge 3.
Lets try to break it down so you guys know how this function work. First, in onCreate method i have button that ready to be trigger if its been pressed by user and once the user enter the string, it will get the input from the editText element and finally passed it to the solve_chal3 function now this where the real deal going to take a place.
single byte XOR means its only encrypted with only one character from ASCII letter thus all we need to do is just brute force by creating a loop that try all character from the ascii table.
and after its done try all the possible key it will append to the variable result for the final result. The following program will generate an output like this
There we go ! we got the original string "cooking mc's like a pound of bacon" and the secret character is 88
Challenge 4:
Description:
Fortunately the challenge has almost the same task in challenge 3 but the different is that rather than decrypting one lousy string it expected us to decrypted 327 strings from the file that have been encrypted with single byte XOR and find which one of it is the real string. Like finding a needle in the haystack
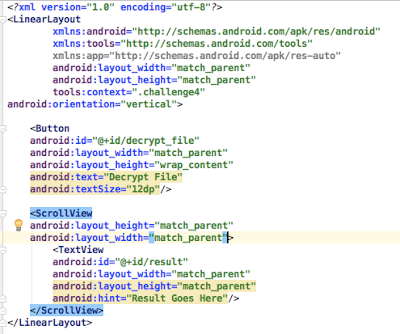
Again i just going to make the UI really simple is just comprise with a button and scroll view.
The following is the code that i create to finish the challenge. First i create a listener a button that will call a function called set4_solves(). Its responsible to load the file that contain encrypted string and brute force until find the right secret using cal_english_score function. In kotlin you can load the file by the following syntax:
applicationContext.resources.openRawResource(R.raw.chall_4).bufferedReader().user{
it.forEachLine{
} => iterate every line, the it variable act as a cursor that will contain the each of the line
}
in cal_english_score function i just copy paste the previous code from challenge 3 but we don't want exhaust the resources to show all the result of brute force so i put an extra line of code that do a check of string if they have an English letter once we have hit it will append to the result variable and show it to the user
yea we got the secret string. TBH i don't recommend you guys to run the code on the vm or real phone device i try it once and it cost me a lot of time waiting (20 minutes ) because our approach is using O(n2) i suggest you guys to try solve this challenge with other programming language like python. I also create a python version of this code:
#One of the 60-character strings in this file has been encrypted by single-character XOR.
#Find it.
#have to use python enchant to detect english word
import enchant
import binascii
import string
import sys
alpha = string.ascii_lowercase
special = string.punctuation
file = open("4.txt","r")
file_encrypted = file.readlines()
d = enchant.Dict("en_US")
def single_xor(string_s,key):
result = ""
for x in string_s:
result += chr(ord(x) ^ key)
return result
data_index = 0
counter = 0
for e in file_encrypted:
encrypted = binascii.unhexlify(e.rstrip("\n"))
for x in range(0,256):
counter += 1
data = single_xor(encrypted,x)
score = 0
for x in data:
if x in alpha:
score += 1
if score > 10:
if (" " in data):
temp = data.split(" ")
try:
if d.check(temp[0]) and len(temp[0])>1:
print data
except:
pass
Thank you :)













Comments
Post a Comment